Online Banking with Bank of America 18 years, 8 months ago by Martey Dodoo
Netcraft recently wrote an article about online banking websites switching away from SSL login forms toward less secure login pages. Back in May, Mozilla programmer Jesse Ruderman wrote about the same issue. My bank, Bank of America, defends the practice by claiming:
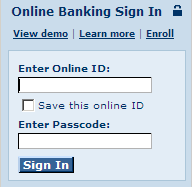
The moment you click Sign In and before your ID and passcode leave your computer, we encrypt them using Secure Sockets Layer (SSL) technology. That means only Bank of America has access to your ID and passcode.
This is disingenous. When you submit your ID and password at the non-SSL Bank of America website, it directs the data to https://onlineid.bankofamerica.com/cgi-bin/sso.login.controller. Under normal circumstances, this is fine.
Of course, security exploits are all about creating abnormal circumstances. The non-SSL Bank of America homepage commits what Internet Explorer developer Eric Lawrence calls "Critical Mistake #1" in its implementation of SSL:
There are two problems with this practice: One fairly obvious, and one slightly less obvious. The first problem is simple: How does the user know that the form is being submitted via HTTPS? Most browsers have no such UI cue. (Pretty much everyone turns off the "Warn when sending unencrypted form data" option within 2 minutes of installing the browser.) Even supposing there was a UI cue that the form was targeted at a HTTPS page, how could the user know that it was going to the right HTTPS page? If the login form was delivered via HTTP, there's no guarantee it hasn't been changed between the server and the client. A bad guy sitting on the wire between the two could simply retarget the POST to submit to a HTTPS site that he controls. Oops.
If you are a customer with an account at Bank of America or another bank which does not use SSL login forms, you are probably thinking that "oops" is not good enough when it comes to your financial information. I would agree with you. After a troubling discussion with Bank of America's customer service[1], a customer service representative told me that my concerns had been forwarded to their technical team. That was a week ago.
In the meantime, you can use this SSL version of the Bank of America login page.
[1] When I explained why Lawrence's example of a man-in-the-middle attack involving malicious DNS servers was a hypothetical problem, I received a boilerplate response for phishing inquiries, explaining that "the website I had visited was not operated by Bank of America" and that I should call them if I had submitted any of my banking information. Since I had both clearly noted that the example was hypothetical, and provided a link to the IEBlog post, this response made me consider closing my account. If Bank of America's customer service representatives do not take the time to even read customer inquiries, how much care are they taking with my money?